Audit & Compliance
Weavestream maintains an append-only audit log of every mutation in the system. The log is tamper-resistant at the database-role level and accessible to SUPER_ADMIN users via a filterable, paginated UI.
What Gets Logged
Every create, update, delete, archive, and restore operation writes an audit entry. Each entry captures:
For sensitive operations (password reveals, credential access), the before/after blobs contain metadata only — plaintext secrets are never written to the audit log.
Tamper Protection
The audit table is protected at the Postgres database-role level:
- The application's database role has
INSERT-only access to the audit table — noUPDATEorDELETE. - Rewriting or deleting audit history requires direct Postgres superuser access — it cannot be done through the Weavestream API or admin UI.
This means even a fully compromised operator account cannot cover its tracks.
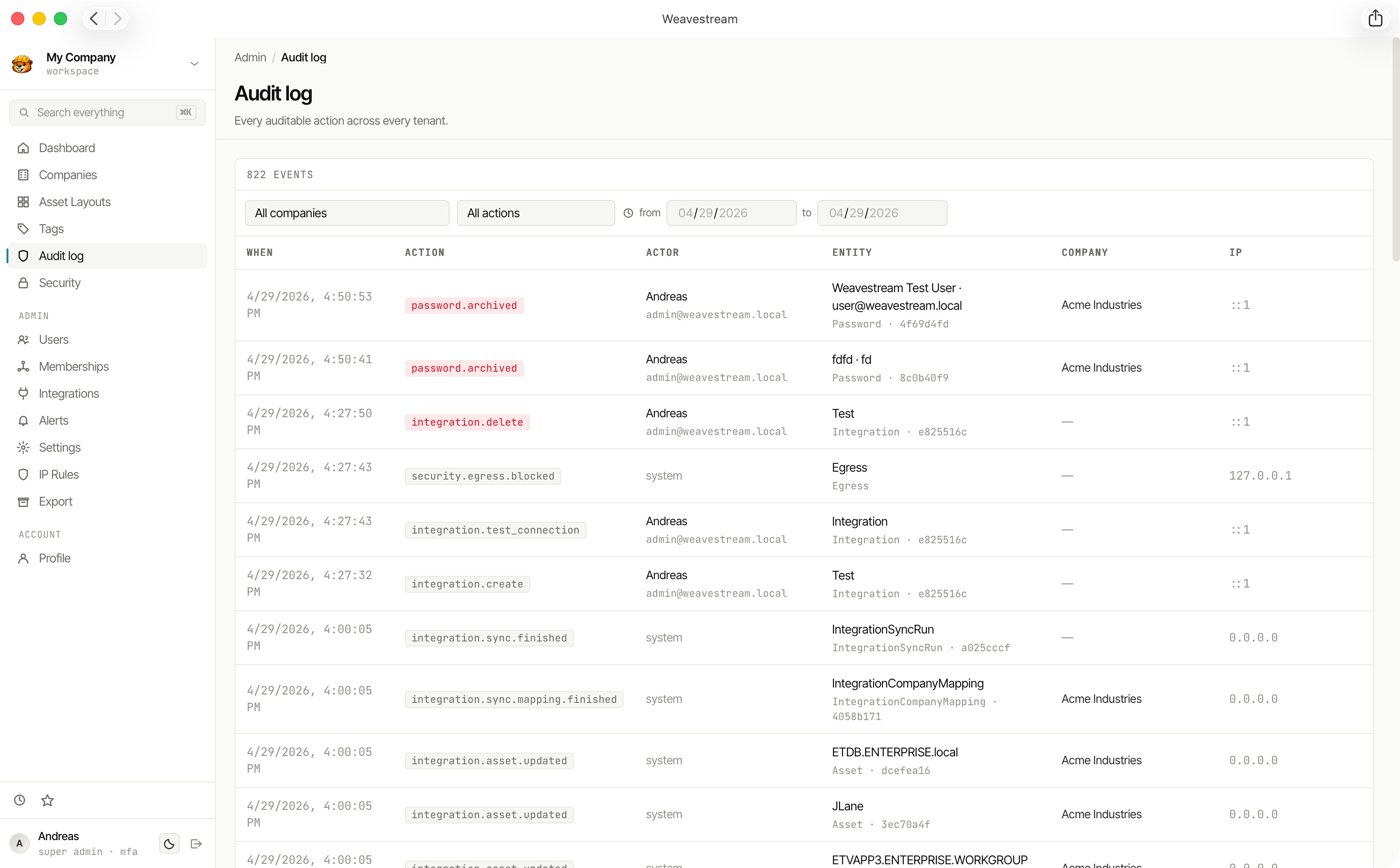
Audit UI
The audit log is accessible at /admin/audit for SUPER_ADMIN users. Features:
- Server-side cursor pagination — efficient for very large audit tables
- URL-sticky filters — filter by date range, actor, action type, and entity type; filters persist in the URL for sharing and bookmarking
- Configurable page size
- Before/after diff view — expandable JSON diffs for each entry
Password Reveal Audit
Password decryptions are a special audit category. Every time a credential's secret is revealed to a user, a reveal audit entry is written with the actor, timestamp, IP, and password ID. This creates a complete access trail separate from the general audit log.
Retention
Audit records are never deleted or archived by the application. Retention management (e.g. partitioning old entries to cold storage) is left to the operator as a database-level operation.
Compliance Use Cases
The audit log and security model support several common compliance requirements: